Brad Sams (my boss at Petri.com) published a story last night about how Microsoft has started to push out Windows 10 upgrades to domain-joined PCs.
Note that the PC doesn’t upgrade via Windows Update; the user will be prompted if they want to update, and then a deliberately confusing screen “encourages” the user to upgrade.
Brad notes that the environment must meet certain requirements:
- The machine must be running and licensed for Windows 7 Pro or Windows 8.1 Pro (Enterprise doesn’t do this stuff).
- There is no WSUS, ConfigMgr, etc – the machine gets updates directly from MSFT – this means smaller businesses for the most part.
- The machine must be a domain member.
As you can see, this affects SMEs with a domain (no WSUS, etc). But I’d be surprised if larger businesses weren’t targeted at a later point in order to help MSFT hit their 1 billion PCs goal.
In my opinion, this decision to push upgrades to business is exactly the sort of action that gives Microsoft such a bad name with customers. Most SMEs won’t know this is coming. A lot of SMEs run systems that need to be tested, upgraded, or won’t support or work on newer operating systems. So Microsoft opting to force change and uncertainty on those businesses that are least ready is down right dumb. Brad reports that Microsoft claims that people asked for this upgrade. Right – fine – let those businesses opt into an upgrade via GPO instead of the other way around. Speaking of which …
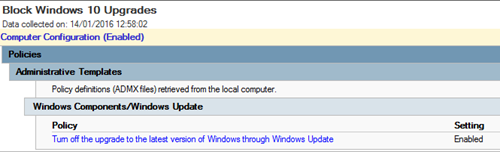
There is a blocker process. I work in a small business and I’ve deployed the blocker. Windows Update added new GPO options to our domain controllers, and I enabled the GPO to block Windows upgrades via Windows Update:
As you can see – I’ve deployed this at work. We will upgrade to Windows 10 (it’s already started) but we will continue to do it at our own pace because we cannot afford people to be offline for 2 hours during the work day while Windows upgrades.

I have a WS2008R2 DC, no pending Windows Updates, and I do not see this GPO.
You should have. Click the link and read about the blocker for yourself.
OK, its working now. I had to manually download & apply the update, then copy WindowsUpdate.admx & WindowsUpdate.adml to the sysvol location.
Interestingly if you use a central policy store in SYSVOL and have already updated your ADMX/ADML files to the Windows 10 versions, this setting isn’t present. Microsoft appears to have removed it from the files (at least the v1511 ones). It makes it seem like they expect you to move your entire fleet to Windows 10 at the same time and without pre-testing on your production domain(s)…
I ended up merging the the entries from the “old” July 2015 Windows Update files into the v1511 ones so that I could configure this setting. I then discovered that I had already configured it before we upgraded the files in the policy store and it was just hidden from view in GPMC 🙂