Smell that? We’re getting close to release! Microsoft has released a bunch of technical documentation downloads for System Center 2012:
- Technical Documentation Download for System Center 2012 – Operations Manager
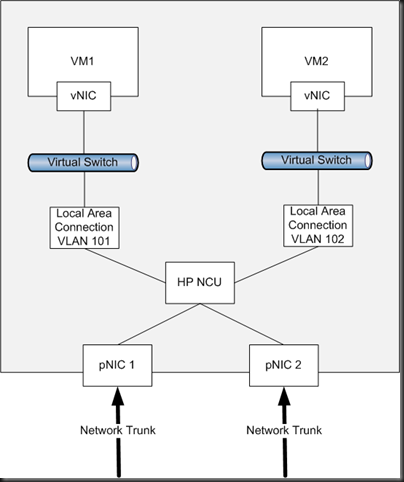
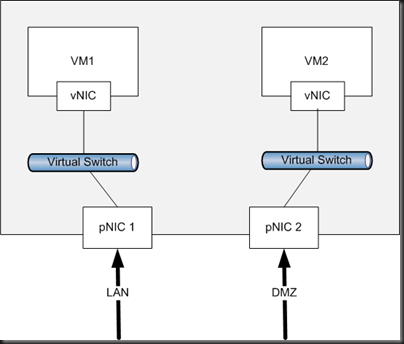
- Technical Documentation Download for System Center 2012 – Virtual Machine Manager
- System Center 2012 Configuration Manager
- Technical Documentation Download for System Center 2012 – Orchestrator
- Technical Documentation Download for System Center 2012 – Service Manager
- Technical Documentation Download for System Center 2012 – Unified Installer
And there’s a lot of related downloads available too:
- Microsoft Security Compliance Manager: Take advantage of the experience of Microsoft security professionals, and reduce the time and money required to harden your environment. This end-to-end Solution Accelerator will help you plan, deploy, operate, and manage your security baselines for Windows client and server operating systems, and Microsoft applications. Access the complete database of Microsoft recommended security settings, customize your baselines, and then choose from multiple formats—including XLS, Group Policy objects (GPOs), Desired Configuration Management (DCM) packs, or Security Content Automation Protocol (SCAP)—to export the baselines to your environment to automate the security baseline deployment and compliance verification process. Use the Security Compliance Manager to achieve a secure, reliable, and centralized IT environment that will help you better balance your organization’s needs for security and functionality.
- System Center 2012 – Service Manager Component Add-ons and Extensions: Download and install add-ons and extensions for the System Center 2012 – Service Manager component.
- System Center 2012 – Orchestrator Component Add-ons and Extensions: Download and install add-ons and extensions for the System Center 2012 – Orchestrator component.
And there are some new management packs too! Check the catalog, read the documentation, prep, download, import, and configure as specified in that documentation you made sure to read first, rather than lazily importing the management packs via the import GUI and hoping for the best ![]()